Top 10 Cybersecurity Interview Questions to Master in 2026

Landing a top cybersecurity role isn't just about knowing acronyms; it's about proving you can think critically under pressure, communicate complex risks, and solve real-world problems. Recruiters are moving beyond textbook definitions to find practitioners who blend deep technical knowledge with sharp business acumen and practical incident response skills. This guide is your playbook, designed to prepare you for the multifaceted challenges of the modern security interview.
This comprehensive listicle breaks down the most critical cybersecurity interview questions you'll encounter, covering the full spectrum of inquiry:
- Technical Deep Dives: From the OSI model to zero-trust architecture.
- Behavioral Assessments: Proving your experience with real-world examples.
- Scenario-Based Challenges: Demonstrating your thought process in high-stakes situations.
For each question, we move beyond generic advice. You'll get a breakdown of the interviewer's intent, a concise sample answer, likely follow-up questions, and actionable preparation tips. We'll also explore accessibility and pacing strategies for neurodivergent candidates to confidently showcase their skills. You will learn how to articulate your value clearly and effectively, ensuring you are prepared to demonstrate not just what you know, but how you apply it. Let's get you ready to demonstrate your true capabilities and secure your next role.
1. Technical: Explain the OSI Model and Its Relevance to Cybersecurity
This is one of the most foundational cybersecurity interview questions because it tests your core understanding of network architecture. The Open Systems Interconnection (OSI) model is a conceptual framework that standardizes the functions of a telecommunication or computing system into seven distinct layers. Interviewers ask this to gauge your ability to think systematically about how data moves and where vulnerabilities can emerge.
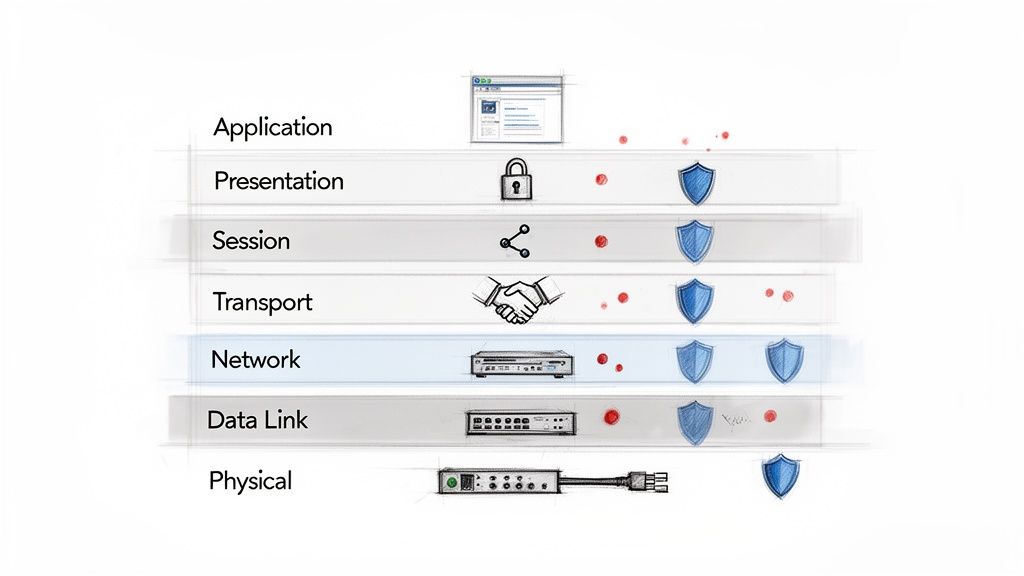
A strong answer goes beyond just listing the seven layers (Physical, Data Link, Network, Transport, Session, Presentation, Application). It connects each layer to specific security controls and threats, demonstrating that you see the model not as an academic exercise, but as a practical tool for building a defense-in-depth strategy.
What the Interviewer Wants to See
- Systematic Thinking: Can you break down a complex system into its components?
- Practical Application: Can you connect theoretical knowledge to real-world security threats like DDoS attacks, man-in-the-middle attacks, or SQL injection?
- Depth of Knowledge: Do you understand the why behind security measures, not just the what?
How to Prepare Your Answer
- Structure Your Explanation: Start with a brief, one-sentence definition of the OSI model. Then, walk through the layers, but instead of just naming them, provide a security context for two or three key layers.
- Use Specific Examples: Connect layers to tangible threats and controls. For instance, explain that firewalls primarily operate at Layer 3 (Network) and Layer 4 (Transport) to filter traffic based on IP addresses and ports. Mention that encryption at Layer 6 (Presentation) protects data confidentiality.
- Frame it as a Diagnostic Tool: Emphasize that you use the OSI model to troubleshoot issues and analyze threats. For example: "When investigating a potential breach, I use the OSI model to methodically check for vulnerabilities, starting from the physical layer and moving up."
- Connect to Your Experience: If you worked on a network segmentation project, tie it back to Layer 3. This grounds your theoretical knowledge in practical experience, making your answer more compelling.
2. Technical: What is the Difference Between Symmetric and Asymmetric Encryption?
This is a fundamental cryptography question designed to test your understanding of core data protection principles. Interviewers use this prompt to evaluate your knowledge of how encryption works, its practical applications, and the trade-offs involved. Your answer reveals whether you can move beyond buzzwords and discuss the mechanics of securing data in transit and at rest.
A strong response will clearly define both symmetric and asymmetric encryption, explain their key differences, and provide real-world use cases for each. This demonstrates that you understand the "why" behind cryptographic choices, not just the "what," which is critical for any role involving secure communications or data storage.
What the Interviewer Wants to See
- Conceptual Clarity: Can you articulate the core difference involving the number of keys used?
- Practical Application: Can you connect each encryption type to specific technologies like TLS, PGP, or database encryption?
- Understanding of Trade-offs: Do you recognize why one is used over the other in certain scenarios (e.g., speed vs. key management)?
How to Prepare Your Answer
- Structure Your Explanation: Start with a clear, concise definition for each. For symmetric, say: "It uses a single shared key for both encryption and decryption." For asymmetric, say: "It uses a key pair, a public key to encrypt and a private key to decrypt."
- Use a Hybrid Example: The best way to demonstrate practical knowledge is by explaining how they work together. Describe the TLS handshake: "Asymmetric encryption, like RSA, is used to securely exchange a symmetric key at the beginning of a session. The rest of the communication is then encrypted using the faster symmetric algorithm, like AES."
- Discuss Key Management: Briefly touch upon the primary challenge of each. Symmetric encryption's challenge is secure key distribution, while asymmetric encryption's challenge is verifying the authenticity of public keys (solved by Certificate Authorities).
- Connect to Your Experience: Ground your answer in your own work. For example: "In my last role, I was responsible for managing TLS certificates for our web applications, which involved handling the public-private key pairs used in asymmetric encryption. We also used symmetric AES-256 to encrypt customer data at rest in our databases." This links theory to tangible, valuable experience.
3. Technical: What is SQL Injection and How Do You Prevent It?
This is one of the most classic and critical cybersecurity interview questions, especially for roles touching application or web security. SQL Injection (SQLi) is a code injection technique where an attacker inserts malicious SQL statements into an entry field for execution. Interviewers use this question to assess your practical understanding of a top-tier threat and your grasp of secure coding principles.
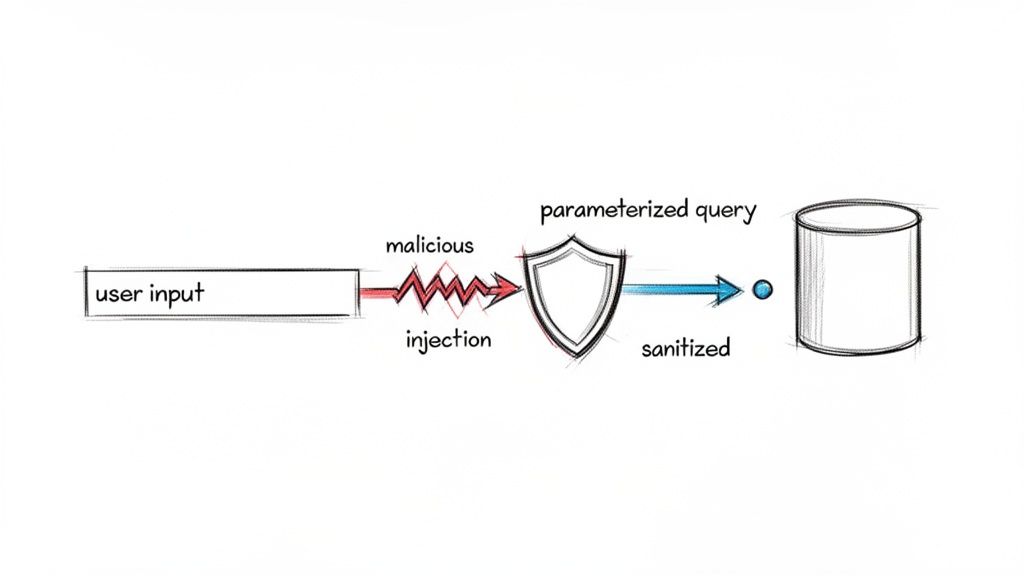
A top-tier answer moves beyond a simple definition. It explains the "how" (e.g., concatenating unsanitized user input into a database query) and the "why it matters" (e.g., data exfiltration, authentication bypass, database takeover). Demonstrating knowledge of a multi-layered defense strategy shows you think like a seasoned security professional, not just a textbook learner.
What the Interviewer Wants to See
- Offensive and Defensive Mindset: Can you explain how the attack works and, more importantly, how to build robust defenses against it?
- Practical Coding Knowledge: Do you understand concepts like parameterized queries, input validation, and Object-Relational Mapping (ORM) frameworks?
- Defense-in-Depth Approach: Can you articulate a layered security strategy that includes more than one single control?
How to Prepare Your Answer
- Structure Your Explanation: Start with a clear, concise definition of SQL injection. Then, provide a simple, concrete example of a vulnerable query (e.g., SELECT * FROM users WHERE username = ' + userInput + ';).
- Detail Multiple Preventions: Lead with parameterized queries (prepared statements) as the primary defense. Then, add other layers like input validation to reject malicious characters, using ORMs that handle sanitization automatically, and implementing a Web Application Firewall (WAF) to block common attack patterns.
- Frame it with Business Impact: Connect the technical threat to business risk. For example, "A successful SQL injection doesn't just compromise a table; it can lead to a full data breach, exposing sensitive customer PII, causing massive reputational damage, and incurring regulatory fines."
- Connect to Your Experience: Mention specific tools or frameworks you've used. For instance, "In my last role using Django, its built-in ORM helped us mitigate SQLi risks by abstracting away raw SQL queries. We also used a WAF for an additional layer of protection."
4. Behavioral: Tell Me About a Time You Identified and Resolved a Critical Security Vulnerability
This is one of the most critical cybersecurity interview questions because it moves beyond theory into real-world impact. This behavioral prompt is designed to evaluate your problem-solving skills, technical judgment, initiative, and communication under pressure. Interviewers use it to see if you can articulate a complex technical event as a clear, structured story with a measurable business outcome.
A great answer showcases a full cycle of security practice, from proactive discovery to collaborative remediation and post-mortem learning. It demonstrates that you think like a true security professional, focusing not just on closing a ticket but on reducing organizational risk and strengthening defenses for the future.
What the Interviewer Wants to See
- Problem-Solving Process: Can you logically break down a vulnerability, assess its risk, and develop a remediation plan?
- Technical Acumen and Initiative: Did you discover the flaw through your own analysis, or did you simply follow a process? How did you validate the vulnerability?
- Communication and Collaboration: How did you communicate the risk to stakeholders, and how did you work with other teams (like developers or infrastructure) to implement a fix?
- Impact and Ownership: Can you quantify the positive result of your actions and show that you learned from the experience?
How to Prepare Your Answer
- Structure with the STAR Method: Frame your story using Situation, Task, Action, and Result. Set the scene (Situation), define your goal (Task), detail the specific steps you took (Action), and quantify the outcome (Result).
- Quantify Your Impact: Use concrete numbers. Instead of saying "it affected some servers," say "it exposed three production web servers hosting customer data." Instead of "we fixed it quickly," say "we deployed a patch within a 4-hour maintenance window."
- Highlight Soft Skills: This isn't just a technical story. Emphasize how you communicated with non-technical managers, collaborated with the incident response team, or wrote clear documentation to prevent a recurrence.
- Show Growth: Conclude by explaining what you learned. For example: "This incident highlighted a gap in our code review process, so I worked with the DevOps team to integrate a static analysis tool into our CI/CD pipeline, which now catches similar issues automatically."
5. Behavioral: Describe a Time You Had to Communicate a Complex Security Issue to Non-Technical Stakeholders
This is one of the most critical cybersecurity interview questions for any role beyond entry-level, as it tests your communication and influence skills. An attacker only needs to find one flaw, but a security professional needs to convince an entire organization to build a resilient culture. Interviewers use this question to see if you can translate technical jargon into business impact, a vital skill for gaining buy-in for security initiatives.
A strong answer demonstrates empathy, strategic thinking, and the ability to frame security not as a blocker, but as a business enabler. It shows you understand that your technical expertise is only effective if you can persuade others to act on it. This question reveals your potential to lead, manage risk, and align security goals with organizational objectives.
What the Interviewer Wants to See
- Business Acumen: Can you connect a technical vulnerability, like Log4j, to tangible business risks like financial loss, reputational damage, or operational downtime?
- Empathy and Influence: Do you understand the priorities and pressures of non-technical teams (e.g., Marketing, Sales)? Can you tailor your message to resonate with their goals instead of just listing technical facts?
- Clarity and Conciseness: Can you distill a complex topic into a clear, actionable summary without oversimplifying or causing unnecessary panic?
How to Prepare Your Answer
- Structure with STAR: Use the Situation, Task, Action, Result (STAR) method to frame your story. Clearly outline the complex security issue, your role in communicating it, the specific actions you took, and the positive business outcome.
- Use Analogies and Metrics: Avoid technical jargon. Instead of "cross-site scripting," you might say, "a vulnerability that could allow an attacker to impersonate our users on our website." Quantify the risk and the solution using business metrics, for example, "The cost of a potential breach was estimated at $X, while the cost of implementing this control was only $Y."
- Focus on Collaboration: Frame your approach as a partnership. Show that you presented options and respected business constraints, rather than issuing rigid demands. For instance, "I explained the risk and collaborated with the product team to find a solution that secured the feature without delaying the launch."
- Highlight the "So What?": Conclude by explaining what you learned from the experience. A great closing statement might be, "This taught me the importance of involving security earlier in the development lifecycle, which led me to champion a 'shift-left' security initiative in my next project." This demonstrates strategic thinking and a commitment to continuous improvement.
6. Scenario-Based: You Detect Suspicious Data Exfiltration Activity at 2 AM. Walk Me Through Your Response.
This is a classic scenario-based question designed to test your incident response (IR) methodology, decision-making under pressure, and technical judgment. Interviewers use cybersecurity interview questions like this to see if you can move beyond theory and apply a structured, logical process during a crisis. It reveals your maturity, prioritization skills, and ability to balance immediate technical actions with broader business impact.
This question isn't just about listing tools; it’s about demonstrating a coherent, repeatable incident-handling process. A strong answer shows you can identify, contain, and analyze a threat methodically, even when the clock is ticking and the stakes are high.
What the Interviewer Wants to See
- A Systematic IR Process: Can you follow a recognized framework (like NIST or SANS) without getting lost in the details? They are looking for the six phases: Preparation, Identification, Containment, Eradication, Recovery, and Lessons Learned.
- Technical Acumen: Do you know which tools to use and when? Can you articulate why you would use a SIEM alert, EDR data, or firewall logs?
- Calm Under Pressure: Can you communicate your plan clearly and logically without jumping to conclusions or panicking?
- Business Awareness: Do you understand that your technical actions have business consequences? This includes knowing when to escalate and how to communicate with stakeholders.
How to Prepare Your Answer
- Structure Your Response Chronologically: Follow the incident response lifecycle. Start with Identification ("My first step would be to validate the SIEM alert by..."), move to Containment ("Next, I'd isolate the affected host from the network..."), then Investigation, Eradication, and Recovery.
- Reference Specific Tools: Instead of saying "I'd check the logs," say "I'd start by reviewing the raw logs in Splunk that triggered the alert, then pivot to our CrowdStrike EDR to examine the process tree on the endpoint."
- Balance Containment and Forensics: Acknowledge the trade-off between stopping the attack immediately (e.g., shutting down the server) and preserving evidence. Explain your decision-making process: "My priority is containment, so I would isolate the machine from the network, but I would not shut it down immediately to preserve volatile memory for forensic analysis."
- Mention Communication and Escalation: Show you're not a lone wolf. State clearly when you would engage other team members, consult the on-call runbook, or escalate to management. Communication is a critical part of any real-world incident response.
7. Scenario-Based: A Colleague Asks You to Bypass a Security Control to Meet a Deadline. How Do You Handle It?
This is one of the most revealing cybersecurity interview questions because it moves beyond technical skills to assess your ethical judgment, communication, and ability to balance business needs with security principles. This scenario tests how you navigate pressure from peers and your commitment to organizational policy, even when it's inconvenient. Interviewers use this to see if you are a collaborative problem-solver or a rigid gatekeeper.
A strong answer demonstrates empathy for the colleague's deadline pressure while holding firm on security principles. It focuses on finding a secure, alternative path forward rather than simply saying "no." This shows you can act as a business enabler who manages risk, not just an obstacle who blocks progress.
What the Interviewer Wants to See
- Ethical Integrity: Do you prioritize security and company policy over convenience?
- Problem-Solving Skills: Can you propose viable, secure alternatives instead of just rejecting the request?
- Communication & Diplomacy: Can you explain security risks clearly and respectfully without being confrontational?
- Risk Management Acumen: Do you understand when to escalate an issue or document a decision for the record?
How to Prepare Your Answer
- Acknowledge and Empathize: Start by validating your colleague's position. Say something like, "I understand the pressure you're under to meet this deadline, and I want to help us get there." This establishes you as an ally.
- Explain the 'Why': Briefly explain the risk associated with bypassing the control. Frame it in terms of business impact, such as, "Disabling that control could expose sensitive customer data, which would be a much bigger problem for us than a missed deadline."
- Offer Collaborative Solutions: Shift immediately into problem-solving mode. Suggest alternatives like, "Let's explore a few options. Could we set up a temporary, isolated environment for your testing? Or can we work together to find a compliant workaround that still meets your goal?"
- Know When to Escalate: Mention your process for handling unresolved conflicts. A good response includes, "If we can't find a mutually agreeable solution, my next step would be to document the request and the associated risks and bring it to both our managers to make a formal risk-based decision."
8. Technical: Explain Zero-Trust Architecture and How You'd Implement It in a Hybrid Cloud Environment
This is one of the more advanced cybersecurity interview questions, designed to test your grasp of modern security paradigms that move beyond traditional perimeter defense. Zero-Trust Architecture (ZTA) is a security model based on the principle of "never trust, always verify." It assumes that no user or device, whether inside or outside the network, should be trusted by default, requiring strict verification for every access request. Interviewers use this question to assess your architectural thinking and knowledge of cloud security.
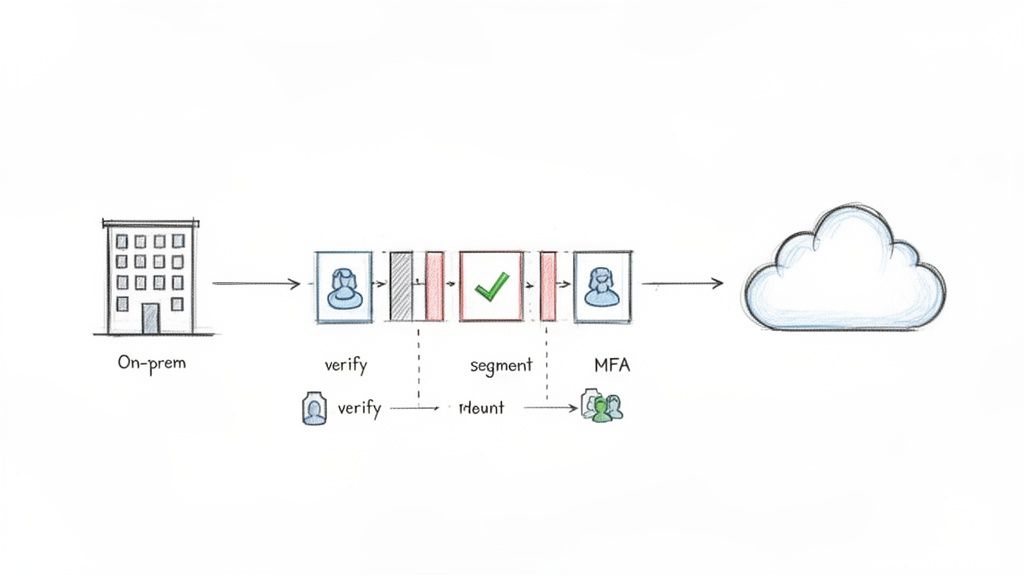
A top-tier answer demonstrates a practical understanding of implementing ZTA in a complex hybrid environment (e.g., on-premises data centers mixed with AWS, Azure, or GCP). It shows you can translate a conceptual framework like the one defined by NIST into a tangible security strategy involving specific technologies and controls, from identity management to micro-segmentation.
What the Interviewer Wants to See
- Modern Security Acumen: Do you understand the shift from perimeter-based security to identity-centric models?
- Architectural Thinking: Can you design a cohesive security strategy that spans disparate environments like on-prem and public clouds?
- Practical Implementation Knowledge: Can you name the specific technologies (IAM, MFA, SASE) and processes needed to build a zero-trust environment?
- Business Awareness: Do you recognize the trade-offs between implementing strict security controls and maintaining user productivity?
How to Prepare Your Answer
- Reference a Framework: Begin by defining zero trust and mention a recognized model, such as NIST SP 800-207 or Google's BeyondCorp. This immediately establishes your credibility.
- Outline Key Pillars: Structure your implementation plan around core zero-trust pillars: strong identity verification (IAM, MFA), device validation, micro-segmentation, and continuous monitoring.
- Use Specific Examples: Connect your explanation to real-world tools and experiences. For example, "In my last role, a key step was implementing a centralized IAM solution like Okta to enforce MFA and context-aware access policies across both our on-prem servers and our AWS workloads."
- Discuss Challenges: Show your strategic thinking by acknowledging the difficulties. Mention the importance of change management to get user buy-in and the technical challenge of applying consistent micro-segmentation policies across hybrid cloud infrastructure.
9. Behavioral: Tell Me About a Time You Disagreed With a Security Decision. How Did You Handle It?
This is one of the more challenging cybersecurity interview questions, as it tests your emotional intelligence, communication skills, and professional maturity. Hiring managers aren't looking for a dramatic story of conflict; they want to see if you can advocate for your position with evidence, handle professional disagreement constructively, and ultimately commit to a team decision.
Your response reveals your ability to balance security ideals with business realities. It shows whether you can challenge ideas respectfully and influence others without direct authority, a critical skill in collaborative security environments where you often have to persuade other departments to adopt safer practices.
What the Interviewer Wants to See
- Professional Maturity: Can you disagree without being disagreeable? Can you accept a decision that doesn't go your way?
- Evidence-Based Reasoning: Did you support your position with data, risk analysis, or established frameworks, rather than just personal opinion?
- Collaborative Mindset: Do you demonstrate respect for other perspectives and understand that colleagues may have different priorities or constraints (e.g., budget, operational impact)?
- Growth and Learning: Do you frame the experience as a learning opportunity, regardless of the outcome?
How to Prepare Your Answer
- Structure with STAR: Use the Situation, Task, Action, Result (STAR) method. Situation: Briefly describe the proposed security decision you disagreed with. Task: Explain your objective and why you felt a different approach was better. Action: Detail the steps you took to voice your concerns respectfully, like presenting data or a risk assessment. Result: Explain the final decision, what you learned, and how you moved forward.
- Focus on Data, Not Drama: Avoid making it a personal conflict. Frame your argument around objective evidence. For example, "The initial plan was to use a less secure protocol for data transfer to meet a deadline. I presented a brief analysis showing the potential financial impact of a data breach associated with that protocol and proposed a slightly more complex but secure alternative."
- Show You Understand Trade-Offs: Acknowledge the other side's perspective. You could say, "I understood the project team was under immense pressure to launch, and my suggestion added a day to the timeline. My goal was to make the security trade-off explicit."
- End with a Positive Takeaway: Conclude by highlighting what you learned. "Ultimately, we went with the original plan but added compensating controls. The experience taught me how to better articulate security risks in terms of business impact and the importance of finding a middle ground."
10. Technical: What is Your Approach to Security Testing and Vulnerability Assessment?
This is one of the most practical cybersecurity interview questions because it moves beyond theory and into your hands-on methodology. Interviewers want to understand your process for proactively identifying and evaluating security weaknesses. They're assessing your familiarity with different testing methodologies, your ability to choose the right tools, and how you translate findings into actionable risk mitigation.
A comprehensive answer will outline a structured process, not just list tools. It should cover the entire lifecycle, from initial scoping and threat modeling to testing, analysis, and reporting. This demonstrates that you can own the vulnerability management process and communicate its value to both technical and non-technical stakeholders.
What the Interviewer Wants to See
- Methodical Process: Do you have a repeatable and logical approach to security testing, or is it ad-hoc?
- Tool Proficiency: Can you articulate the difference between static (SAST), dynamic (DAST), and interactive (IAST) testing, and when to use each?
- Risk Prioritization: Can you explain how you would rank vulnerabilities using frameworks like CVSS and consider business context, not just technical severity?
How to Prepare Your Answer
- Structure Your Explanation: Begin by defining your overall philosophy, such as adopting a "threat-informed defense" approach. Then, outline the key phases of your process: reconnaissance, scanning/testing, validation, and remediation reporting.
- Use Specific Examples: Mention specific tools you've used (e.g., "I've used Burp Suite for dynamic analysis of web apps and SonarQube for static code analysis in CI/CD pipelines"). Explain how you would differentiate a true positive from a false positive.
- Frame it as a Cycle: Describe vulnerability management as a continuous cycle, not a one-off task. You might say, "My approach is cyclical, starting with asset discovery and feeding back into the development lifecycle through security champions to prevent similar vulnerabilities in the future."
- Connect to Your Experience: If you found a critical vulnerability like a SQL injection, describe the steps you took. Explain how you validated it without causing damage, documented the finding, and worked with developers to patch it. This shows you can manage the entire remediation process effectively.
Your Next Step: From Preparation to Performance
Navigating the landscape of cybersecurity interview questions requires more than just rote memorization of technical definitions. As we've explored, each question, whether technical, behavioral, or scenario-based, is a deliberate prompt designed to reveal your problem-solving process, your communication style, and your real-world judgment. The goal is not merely to provide the "right" answer but to demonstrate how you think, adapt, and apply your expertise under pressure.
From explaining the practical security implications of each OSI model layer to walking an interviewer through a high-stakes incident response at 2 AM, your ability to connect theory to action is what sets you apart. The strongest candidates use these questions as springboards to share compelling stories backed by tangible results from their resumes. This article has provided the framework; your next step is to populate it with your unique experiences.
Key Takeaways: Beyond the Answers
Before you close this tab and open a new terminal to practice, let's distill the core strategies that will transform your preparation into a standout performance.
- Connect Concepts to Your Career: Never answer a question in a vacuum. When explaining Zero-Trust Architecture, don't just recite its principles. Instead, connect it to a project where you helped implement micro-segmentation or enforced stricter access controls, even if on a small scale. This turns a theoretical answer into a demonstration of practical skill.
- Master the STAR Method for Impact: Behavioral questions are your stage. Use the Situation, Task, Action, Result (STAR) method not as a rigid script, but as a storytelling tool. Quantify your "Results" whenever possible. Instead of saying "I improved security," say "I implemented a vulnerability management process that reduced critical vulnerabilities by 40% over six months."
- Think Like the Interviewer: For every question, ask yourself, "What are they really trying to learn about me?" A question about communicating with non-technical stakeholders isn't just about your communication skills; it’s about your ability to build consensus, advocate for security, and function effectively within a business.
Insight: Your interview is a live demonstration of your security mindset. Every response should reinforce the idea that you are a proactive, strategic, and collaborative security professional who understands that security enables the business, it doesn't just restrict it.
Your Actionable Preparation Checklist
True confidence comes from deep, structured preparation. Move beyond simply reading cybersecurity interview questions and start actively engaging with them. Here is a practical checklist to guide your efforts:
- Map Questions to Your Resume: Take the top 10-15 questions from this guide and link each one to a specific project, accomplishment, or skill listed on your resume. This creates a powerful arsenal of relevant, evidence-based talking points.
- Practice Articulation Out Loud: The bridge between knowing an answer and explaining it clearly is built by practice. Record yourself answering questions. Listen back to catch rambling, overuse of filler words, or areas where your explanation is unclear. This simple act can dramatically improve your fluency and confidence.
- Simulate Real-World Scenarios: Don't just plan your response to a hypothetical data breach; write it out. What are the first three commands you would run? Who are the first five people you would contact? This level of detail makes your scenario-based answers feel authentic and authoritative.
- Prepare Your Support System: For candidates who are neurodivergent or simply want to reduce cognitive load during a high-stress interview, preparation includes setting up your tools. Organize your key talking points and resume-based examples in a system like Qcard. This allows you to have non-scripted, ethical memory cues available, ensuring you can access your best insights on demand without the pressure of total recall.
By embracing this strategic approach, you shift from being a passive interviewee to an active participant who guides the conversation. You're no longer just answering questions; you are showcasing your value, demonstrating your expertise, and proving that you are the right candidate to protect an organization's most critical assets. The interview is your first security challenge, and with the right preparation, you are more than ready to meet it.
Cybersecurity Frequently Asked Interview Questions
Q: What are the main types of cybersecurity interview questions I should prepare for?
You should prepare for three core types: Technical (testing knowledge of concepts like the OSI model or SQL injection), Behavioral (asking for real-world examples of past experiences), and Scenario-Based (walking through how you would handle a hypothetical security incident).
Q: How should I answer a technical question like "Explain the OSI model"?
Go beyond listing the seven layers. Connect each layer to practical security controls and threats. For example, explain that firewalls operate at the Network and Transport layers, and that encryption protects data at the Presentation layer. This shows you understand its real-world application for defense.
Q: What is the best way to structure an answer to a behavioral question, like describing a past security incident?
Use the STAR method: describe the Situation and Task, detail the specific Actions you took, and conclude with the quantifiable Result of your actions. This creates a clear, compelling story that demonstrates your problem-solving process and impact.
Q: How can I effectively communicate complex security risks to non-technical interviewers or stakeholders?
Avoid jargon and focus on business impact. Use analogies and quantify risks in terms of potential financial loss, operational downtime, or reputational damage. Frame security as a business enabler that supports the organization's goals, not just a technical requirement.
Q: What should I do if I don't know the answer to a technical question in an interview?
Be honest. It's better to admit you don't know than to try to bluff. You can say you aren't familiar with that specific area but are a quick learner, or you can talk through your logical thought process for how you would approach finding the solution.
Ready to transform your interview preparation from a stressful memory test into a confident performance? Qcard provides a smart, ethical way to surface your best resume-grounded talking points during live interviews, reducing cognitive load and helping you articulate your expertise clearly. Stop memorizing and start demonstrating your true value by visiting Qcard to see how it works.
Ready to ace your next interview?
Qcard's AI interview copilot helps you prepare with personalized practice and real-time support.
Try Qcard Free